
Keychains.dev is a secure credential proxy for AI agents. Use "keychains curl" as a drop-in for curl — just replace hard-coded credentials with template variables like {{GITHUB_TOKEN}}. Keychains injects real credentials server-side. Your agent never sees raw secrets — immune to prompt injection by design. Users approve each permission with one click and can revoke access anytime. Full audit trail. Works with 11,000+ API providers (OAuth, API keys, basic auth).see more
Founder
Screenshots



About
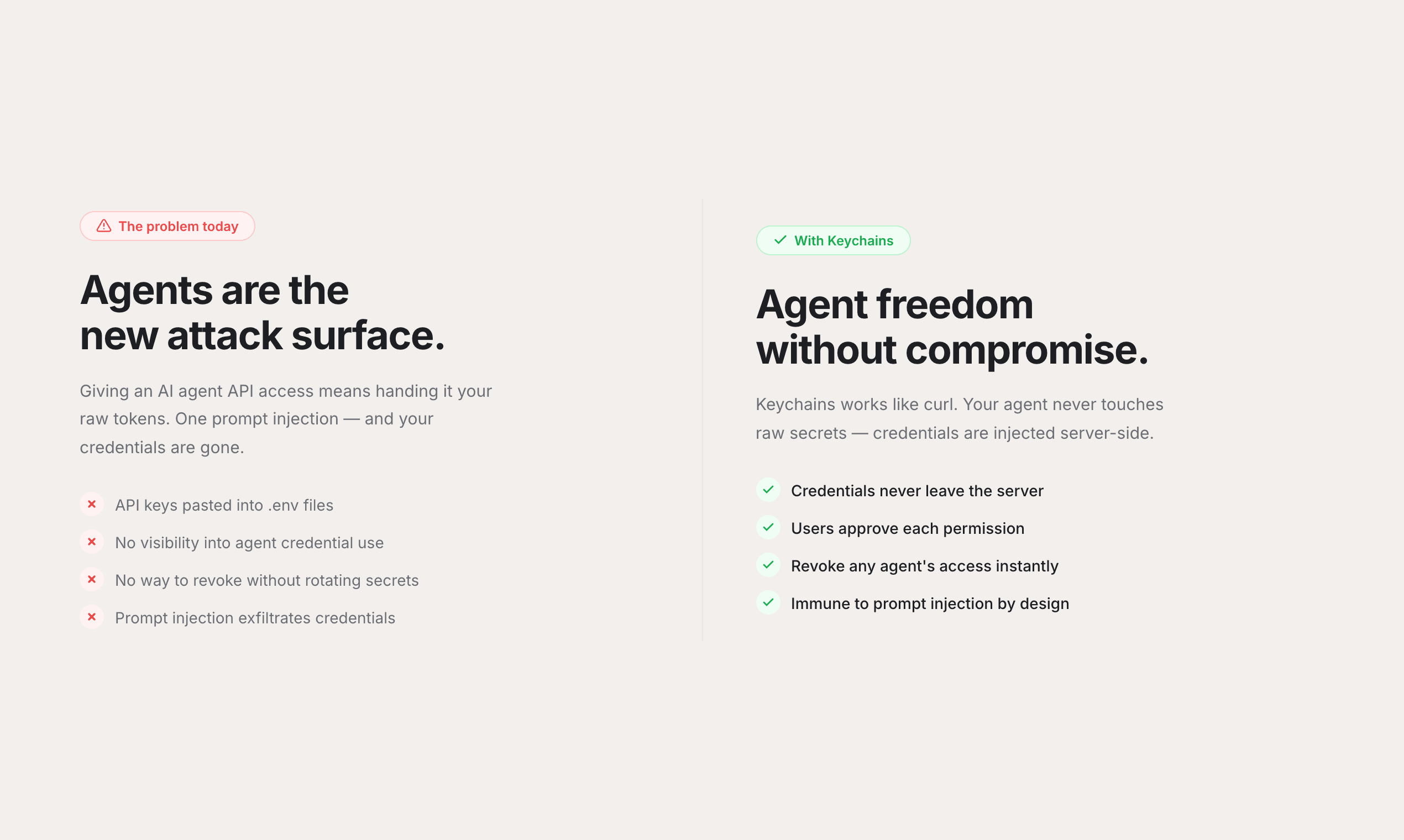
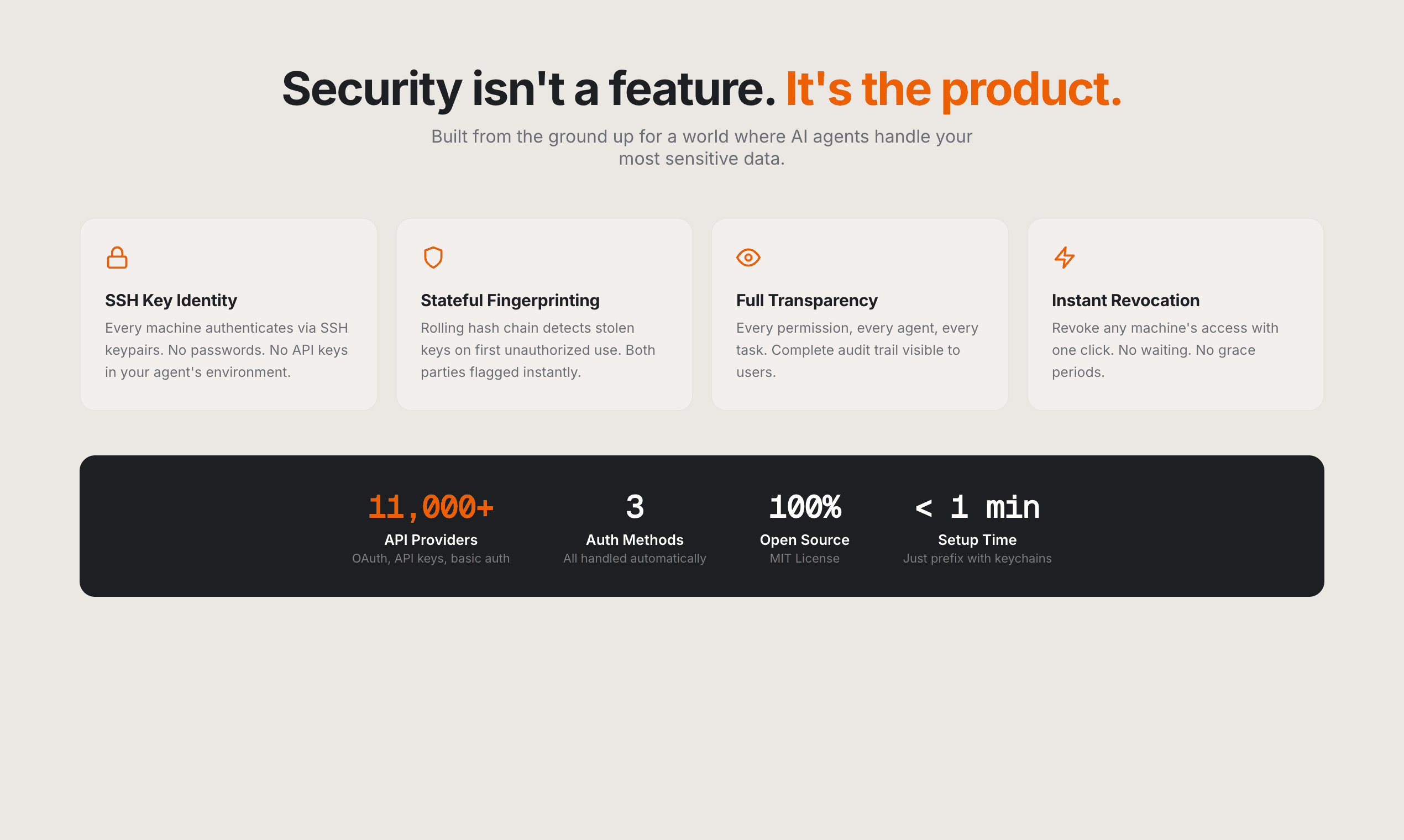
Imagine giving your artificial intelligence agents the power to interact with the vast digital world—accessing everything from GitHub repositories to complex financial data—without ever risking exposure of your most sensitive secrets. That is the core promise of 6.keychains.dev. This isn't just another security layer; it’s a fundamental shift in how AI interacts with external services. Think of it as the ultimate secure handshake between your intelligent systems and the thousands of APIs that power modern applications. Instead of embedding hard-coded tokens, keys, or passwords directly into your agent’s code or prompts—a major security vulnerability—you simply use a placeholder like {{MY_API_KEY}}. Keychains.dev acts as a sophisticated, invisible proxy, handling the credential exchange server-side. Your agent sends the request, Keychains injects the real, verified secret at the last possible moment, and the transaction completes securely. This design makes your AI inherently immune to prompt injection attacks aimed at extracting credentials, offering peace of mind that traditional methods simply cannot match. It’s like giving your AI a secure, temporary keycard for every door instead of handing over the master key.
This system is built for developers who demand both power and absolute control. With support for over 11,000 API providers utilizing standard authentication methods like OAuth, API keys, and basic authentication, the possibilities for extending your AI's capabilities are nearly limitless. The setup is designed to feel instantly familiar; for developers already using command-line tools, keychains.dev offers a drop-in replacement for the standard curl command, simply using "keychains curl" instead. This seamless integration means minimal disruption to existing workflows while instantly elevating your security posture. Furthermore, user control remains paramount. Every permission granted to an agent is explicitly approved by you with a single click, and that access can be revoked just as easily at any time. This granular, on demand control, backed by a comprehensive audit trail, ensures you always know exactly what your AI is accessing and when.
Ultimately, 6.keychains.dev transforms your AI agents from powerful but potentially risky tools into trustworthy digital colleagues. It removes the paralyzing fear associated with giving AI access to real data, unlocking true automation potential. Whether you are building complex data pipelines, automating customer service integrations, or developing cutting-edge applications, securing those external connections is non-negotiable. By abstracting away the raw secrets and managing the secure injection process, keychains.dev allows you to focus entirely on the logic and value your AI provides, confident that your foundational security is robust, transparent, and designed specifically to counter the unique threats posed by large language models and autonomous agents.